A pluggable authentication module (PAM) is a mechanism to integrate multiple low-level authentication schemes into a high-level application programming interface (API). PAM allows programs that rely on authentication to be written independently of the underlying authentication scheme. It was first proposed by Sun Microsystems in an Open Software Foundation Request for Comments (RFC) 86.0 dated October 1995. It was adopted as the authentication framework of the Common Desktop Environment. As a stand-alone open-source infrastructure, PAM first appeared in Red Hat Linux 3.0.4 in August 1996 in the Linux PAM project. PAM is currently supported in the AIX operating system, DragonFly BSD,[1] FreeBSD, HP-UX, Linux, macOS, NetBSD and Solaris.
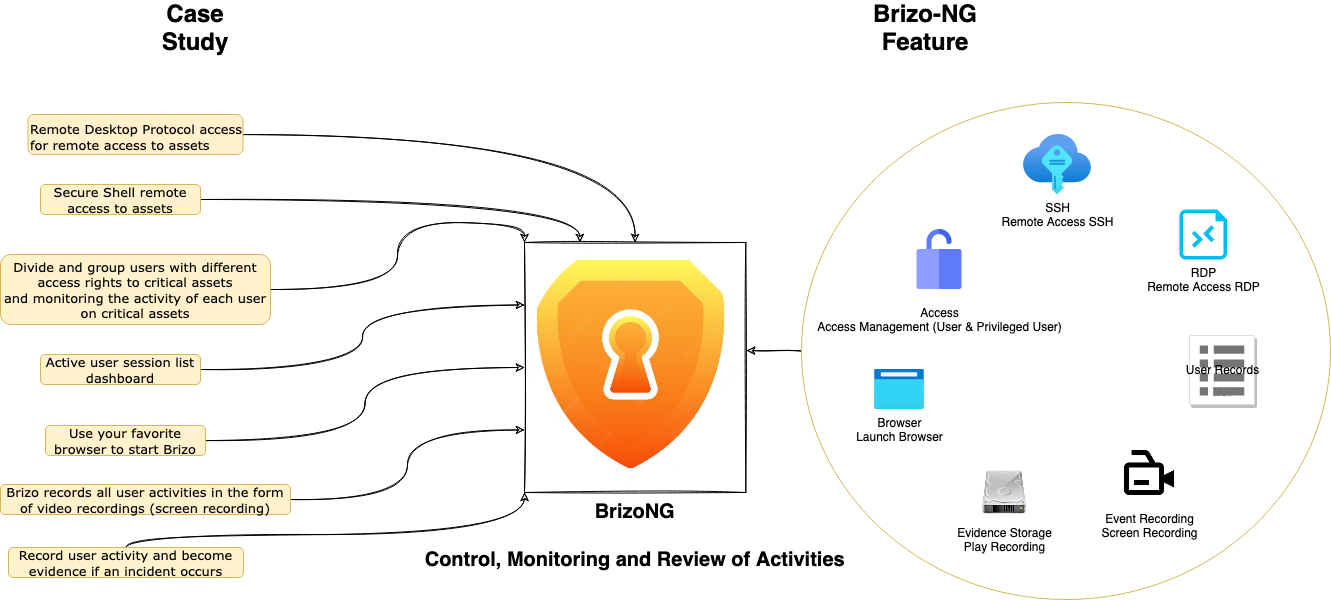
BrizoNG is a fully operational PAM system that can be onboard into your arsenal of security & assets management tools.
Furthermore, in a basic way, access to an asset is granted to a user so that user can do their job. However, it is not uncommon for administrator-level accounts to be the cause of incidents in existing IT systems or cybersecurity incidents. This is because administrator-level access allows for installation, deletion, configuration modification, etc. which, if not properly controlled and supervised, will become incidents in the future.
Access control systems can minimize security risks, such as abuse of authority, damage or loss and data leakage, and misconfiguration
The access control system can make it easier for users to carry out their daily work, with this system access to multiple assets can be done through one centralized platform easily
Access control system can help companies to comply with regulations

As the name implies, the main function of the access control system is to limit user access to existing assets in accordance with specified access rights.
The availability of a feature to monitor active user sessions can help to detect if there is misuse of access by users, so that actions such as disconnecting active sessions or connections can be carried out quickly.
In addition, screen recordings when users conduct sessions with certain assets can make it easier to respond to an incident, the recording can also be used as digital evidence and find the root of the problem if there is a configuration error or become material for future reviews and improvements.
Brizo will be the access management for users who want to remotely session into your infrastructure. The main page of Brizo is a web-based application that can be accessed via the Brizo url address via port 443 (https). Once inside the Brizo application, users can perform remote access either by RDP, SSH, or Telnet to your assets according to the access rights they have. Every remote session made by the user will be recorded in the form of a screen recording video and will be stored on the Brizo server.

Learn how NOOSC delivers insight and innovative technology solutions to take your business to the next level.
LET’S TALK